Blog
P13x13t: The Alias That Redefined Chaos-Based Cybercrime and Digital Identity

The term P13x13t has evolved far beyond a simple hacker alias. It represents one of the most notorious digital identifiers ever linked to large-scale cyber disruption, organized threat campaigns, and cross-border criminal investigations. Once associated with high-impact attacks on platforms like ProtonMail, Roblox, and Hoonigan Industries, the alias eventually transformed into a symbol in academic and technological spaces, influencing discussions around identity masking, generative art, and neural grid structures. The story of P13x13t blends crime, technology, psychology, and cultural evolution, making it one of the most complex digital terms circulating in cybersecurity discourse today.
Origins of P13x13t in the Cyber Underground
P13x13t first gained attention through the activities of the Apophis Squad, an online hacker collective known for chaos-driven cyberattacks. Court records from the United States District Court for the Central District of California and media investigations identified George Duke-Cohan as one of the main individuals behind the alias. Operating under identities such as 7R1D3N7 and DigitalCrimes, Duke-Cohan spearheaded high-profile attacks, often collaborating with American co-conspirator Timothy Dalton Vaughn, known by aliases such as wantedbyfeds and Hacker R US. The pair weaponized the P13x13t handle to amplify their activity, creating a recognizable digital persona that authorities could eventually trace.
How Investigators Unmasked the Operators
The unmasking of P13x13t was not accidental. Investigators from the FBI, NCA, SEROCU, and the U.S. Secret Service conducted deep digital forensics, relying heavily on leaked gaming databases from Blank Media Games, Discord server logs, and analysis by cybersecurity journalist Brian Krebs. These investigations connected login patterns, email traces, and threat signatures directly to Duke-Cohan and Vaughn. Their arrests marked the collapse of the alias as an active cyber-threat identity.
Major Operations Linked to the P13x13t Persona
The P13x13t moniker became infamous for attacks that disrupted major platforms and public institutions. Its operators targeted ProtonMail, launching DDoS waves that prompted the encrypted email service to work directly with law enforcement. They attacked Roblox, demonstrating their botnet-for-hire capabilities, and they extorted Hoonigan Industries, demanding Bitcoin in exchange for restoring normal website operations.
Threat activities escalated into public endangerment when the group used spoofed emails to send bomb threats to more than two thousand schools across the United States and the United Kingdom. Entities such as the UK Department for Education were forced into emergency coordination. Even LAX (Los Angeles International Airport) triggered security protocols after false reports suggested a hijacking on a United Airlines flight.
One of the most chilling elements was a hoax directed at an FBI field office, in which P13x13t actors threatened the release of deadly pathogens. Such actions framed the alias not merely as a digital nuisance but as a genuine national security concern.
Technical and Symbolic Meaning Behind the Identifier
As the cybercases unfolded, the structure of the term P13x13t began receiving attention in academic and technical communities. Developers interpreted the prefix “p” as a reference to protocol or project. The center sequence “13×13” resembles a grid or matrix, a pattern commonly associated with neural networks, data mapping, and generative frameworks. The suffix “t” has been interpreted as token, test, or transmission depending on context.
This structure made the term uniquely suited for reinterpretation. By 2025 and 2026, the alias had shifted into digital folklore. Generative artists used P13x13t as a seed value to create glitch art exploring chaos and symmetry. Privacy advocates cited it as a metaphor for pseudonymity, illustrating how someone can be traceable within a system while remaining conceptually hidden. Developers even began using the term casually in pseudocode as a placeholder or test label, similar to a stylistic “lorem ipsum” for programmers.
Legal Consequences for Individuals Behind the Alias
After years of cyberattacks, both central figures behind P13x13t faced significant prison time. George Duke-Cohan was sentenced in the United Kingdom to three years in prison for mass hoaxes and related crimes. Timothy Dalton Vaughn received a federal sentence of ninety-five months in the United States, influenced not only by his cybercrimes but also by unrelated criminal charges, including possession of illegal content that heightened the severity of his case.
These sentences effectively removed P13x13t from the global cyber threat landscape. By 2026, associated Twitter/X profiles such as @P13x13t and @ApophisSquad were banned, and no new activity emerged from the once-feared alias.
Why P13x13t Still Matters in 2026
Even though the original operators are inactive, the legacy of P13x13t remains an important point of reference in cybersecurity. Experts compare the old chaos-based methods of the Apophis Squad to modern digital threats powered by agentic artificial intelligence, deepfake social engineering, and supply chain infiltration. The shift indicates that while names like P13x13t belong to a previous era, their cultural footprint continues to shape discussions about anonymity, digital ethics, and threat evolution.
The Rise of Digital Folklore
Terms like P13x13t often outlive their criminal origins. They become symbols in online communities, academic circles, and creative industries. The transformation of the alias from a digital threat into an artistic and analytical reference showcases how the internet redefines meaning and legacy over time.
Frequently Asked Questions
What is P13x13t?
P13x13t is a hacker alias once linked to cyberattacks, mass hoaxes, and DDoS campaigns carried out by individuals tied to the Apophis Squad.
Who operated under the P13x13t name?
The alias was primarily associated with British hacker George Duke-Cohan and at times with American collaborator Timothy Dalton Vaughn.
What platforms did P13x13t target?
The group attacked ProtonMail, Roblox, and Hoonigan Industries, among other public institutions and digital services.
How were the hackers behind P13x13t caught?
They were identified through gaming database leaks, Discord logs, IP traces, and investigative contributions from cybersecurity professionals.
Why is the term used in art and coding today?
Its symmetrical structure and cultural history made it suitable as a seed identifier for generative art and as a pseudocode placeholder.
Is P13x13t still active?
No. The alias became inactive following the arrests and prosecution of individuals associated with the Apophis Squad.
Was P13x13t ever a tech product?
Despite public confusion, the term is not connected to consumer electronics or malware and is often mistakenly associated with model numbers like the OnePlus 13T.
What makes P13x13t historically significant?
It represents a turning point in cybercrime investigation, international law enforcement cooperation, and the evolution of digital identity culture.
Blog
What is 8656696225537? What This 13 Digit Unknown Caller Really Means and How to Stay Safe
What Is 8656696225537?
The number 8656696225537 has become a topic of concern for many phone users who notice it appearing in their call logs. At first glance, it looks like a normal phone number, but in reality, it is not a standard dialable number. It is widely described as a 13 digit technical artifact that shows up when a No Caller ID, Unknown Caller, Private, or Restricted call is revealed or unmasked.
This number is often linked to the keypad translation of the word UNKNOWN. On a phone keypad, letters correspond to numbers, and when certain systems attempt to convert hidden caller information into a numeric format, it can produce a sequence like 8656696225537. Instead of displaying the word Unknown, some networks or tools show this numeric version.
Because of this behavior, the number is not tied to a single caller. It represents a hidden identity rather than a real person or business. However, many reports connect it with suspicious calls, which raises concerns about security and privacy.
Why 8656696225537 Appears on Phones?
The appearance of 8656696225537 usually happens when a hidden call is processed through certain systems. Some users see it after using third party unmasking apps such as TrapCall or Truecaller. These tools attempt to reveal the real number behind a blocked or private call, but instead of showing a clear identity, they sometimes display this numeric string.
Mobile carriers like T-Mobile, Sprint, Verizon, and AT&T also play a role. In some cases, network signals or backend systems translate hidden caller data into this number. Instead of simply labeling the call as Unknown or Private, the system outputs a numeric representation.
Another important factor is the use of VOIP systems. Many robocalls originate from internet based phone systems that do not follow traditional numbering rules. These systems can generate unusual caller ID data, which results in numbers like 8656696225537 appearing in call logs.
Is 8656696225537 a Scam Number or a Technical Code?
It is important to understand that 8656696225537 is not a typical scam number that belongs to a specific person or company. It functions more like a technical code or carrier artifact. However, that does not mean it is harmless.
Many reports associate this number with robocalls, spoofing, and hidden caller activity. Scammers often use No Caller ID features to hide their identity, and when these calls are processed or revealed, they may appear as 8656696225537.
This makes the number a strong warning sign. It signals that the caller is intentionally hiding their identity, which is a common tactic used in fraud. It may also be connected to overseas VOIP gateways and automated robodialers that target large numbers of users.
Common Scam Types
Although the number itself is not a direct source, it is frequently connected to various scam scenarios. One of the most common is the Amazon Prime renewal scam. In this case, callers claim that your Amazon account will be charged or cancelled, and they ask you to press a number to speak with an agent.
Another major category involves impersonation of the Social Security Administration. Scammers pretend to be officials and threaten legal action, claiming your Social Security Number has been compromised. They then demand payment or sensitive information.
Some calls involve banks or financial institutions, including fake representatives of the Federal Deposit Insurance Corporation. These scammers ask for account details under the pretense of verification. Others pose as money managers and try to convince victims to invest or share financial data.
There are also legal and government impersonation scams. Callers claim to be detectives, court officials, or representatives from legal agencies. They create urgency by saying you missed jury duty or are involved in a legal case.
In many situations, scammers request payment through gift cards, wire transfers, or cryptocurrency. These methods are difficult to trace and are commonly used in fraud schemes.
Warning Signs to Watch For
Calls linked to 8656696225537 often follow recognizable patterns. One common sign is the silent call. When you answer, you hear nothing or only background noise. This is often a verification method used by robodialers to check if your number is active.
Another red flag is urgency. Scammers try to pressure you into acting quickly. They may threaten arrest, account suspension, or financial loss if you do not respond immediately. Legitimate organizations such as the IRS, SSA, or banks do not operate this way.
Requests for remote access are also dangerous. Some callers ask you to install software like AnyDesk or TeamViewer to fix a supposed issue. This gives them control over your device and access to personal data.
Unusual payment requests are another warning sign. No real company will ask for payment through gift cards, prepaid cards, or cryptocurrency during an unsolicited call.
How to Block 8656696225537 on iPhone and Android?
Protecting your phone starts with using built in settings. On iPhone, you can enable Silence Unknown Callers by going to Settings, then Phone, and turning on the option. This ensures that calls from numbers not in your contacts go directly to voicemail without ringing.
On Android devices, you can open the Phone app, go to Settings, and find the Blocked numbers section. From there, you can enable the option to block calls from unidentified callers or private numbers. This prevents hidden calls from reaching you.
These settings act like a firewall for your phone. They reduce interruptions and lower the risk of interacting with suspicious callers. Calls that are blocked or silenced still appear in your Recents list, so you can review them later if needed.
Carrier Tools That Help Stop These Calls
Mobile carriers offer additional protection beyond device settings. T-Mobile provides Scam Shield and Scam Block features, which can be activated directly or by dialing #662#. These tools help identify and block scam calls before they reach your phone.
Verizon offers the Call Filter service, which labels suspicious calls and allows users to block them. AT&T provides ActiveArmor, a security app that detects fraud and protects against unwanted calls.
These carrier level tools use network data and advanced filtering to identify patterns associated with robocalls and spoofing. They add an extra layer of defense, especially against calls that might bypass standard device settings.
How to Report 8656696225537 to Authorities?
Reporting suspicious calls is an important step in fighting fraud. In the United States, the Federal Trade Commission collects reports through its fraud system. This helps track patterns and take action against large scale scam operations.
The Federal Communications Commission also handles complaints related to unwanted calls and violations of communication laws. Users can report incidents to help regulators understand how scammers operate.
If a call involves Social Security impersonation, it can be reported to the SSA Office of Inspector General. Mobile carriers also accept reports through their fraud portals and security support systems.
Another common method is using the shortcode 7726, which spells SPAM. By sending details of suspicious activity to this number, users help carriers improve their filtering systems.
Best Ways to Stay Safe
Staying safe requires a combination of awareness and action. Avoid answering calls from unknown or hidden numbers whenever possible. If you accidentally answer and hear silence, hang up immediately.
Never press buttons to opt out of calls, as this can confirm your number is active. Do not share personal or financial information over the phone unless you are certain of the caller’s identity.
Always verify claims independently. If someone says they are from Amazon, a bank, or a government agency, end the call and contact the organization through its official number.
Registering your number with the Do Not Call Registry can reduce legitimate telemarketing calls, although it will not stop all scams. If you suspect identity theft, act quickly and use official recovery resources.
In the end, It should be treated as a warning signal rather than a normal phone number. It represents hidden caller activity that is often linked to robocalls and scams. By using proper settings, carrier tools, and safe habits, you can protect your phone and avoid falling victim to these threats.
FAQs
What is 8656696225537 and why does it appear on my phone?
8656696225537 is not a regular phone number. It is a technical representation of a hidden caller, often shown when a No Caller ID or Private number is revealed by certain apps or network systems.
Is 8656696225537 a scam number or a real caller?
It is not a real caller number. It is more like a system generated code. However, it is commonly linked with scam related calls, so you should treat it as suspicious.
Why do I receive silent calls from numbers like 8656696225537?
Silent calls are often used by robodialers to check if your number is active. If you answer, your number may be marked for future scam attempts.
Can 8656696225537 bypass Do Not Disturb settings?
Some users report that hidden calls linked to this number can bypass Do Not Disturb settings. This usually happens because the caller ID is masked or handled differently by network systems.
How can I block calls related to 8656696225537?
You can block these calls by enabling Silence Unknown Callers on iPhone or blocking unidentified callers on Android. Carrier tools like Scam Shield and Call Filter also help stop such calls.
Are calls from 8656696225537 dangerous?
Yes, they can be risky. While the number itself is not harmful, it is often associated with scams like impersonation, fraud, and phishing attempts.
What should I do if I answered a call from 8656696225537?
If you answered and did not share any information, you are likely safe. Just avoid interacting further. If you shared details, you should monitor your accounts and report the incident.
Where can I report calls from 8656696225537?
You can report these calls to the Federal Trade Commission, the Federal Communications Commission, or your mobile carrier. You can also use the 7726 SPAM method to help carriers track suspicious activity.
Blog
How Many Ounces in a Half Gallon? Complete Guide to US vs UK, Bottle Math, Weight, and Hydration Facts
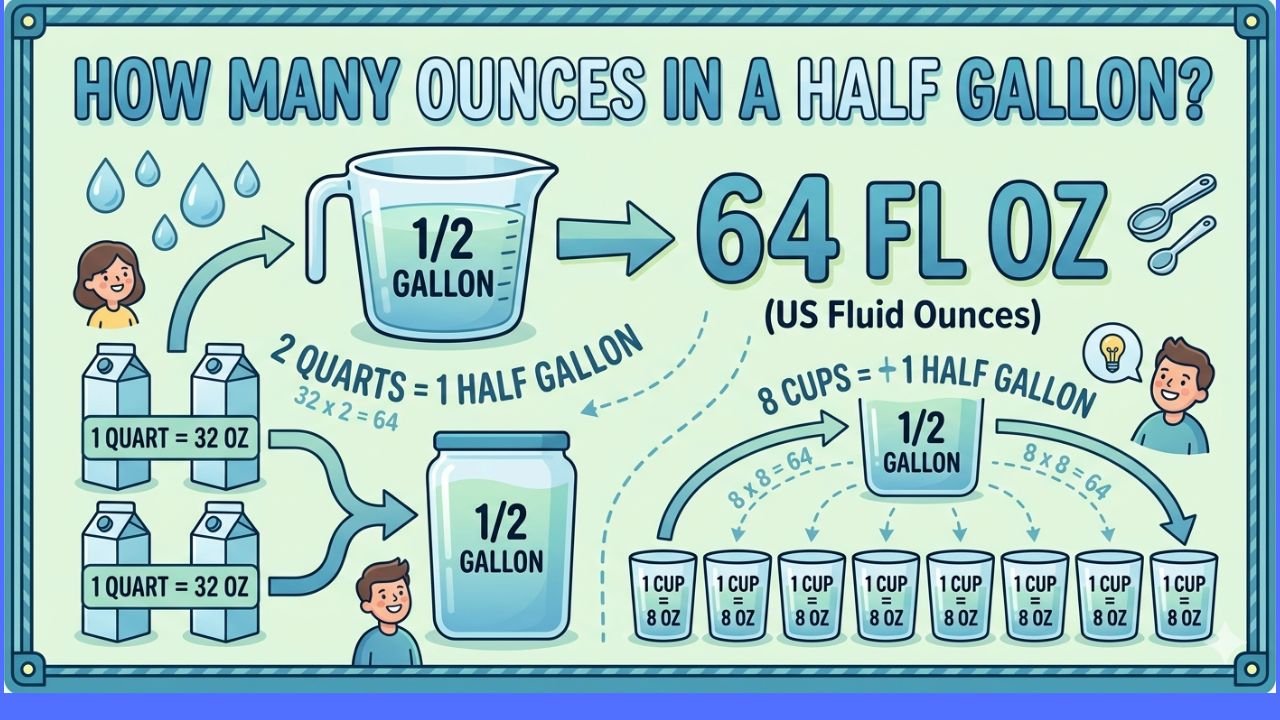
If you are wondering how many ounces are in a half gallon, the simple answer is this. In the United States customary system, a half gallon equals 64 fluid ounces. This comes from the fact that one full US gallon contains 128 fluid ounces, and half of that is 64 oz. This number is widely used in daily life, from drinking water to measuring liquids for cooking and shopping.
A half gallon also equals 8 cups, 2 quarts, 4 pints, and 16 gills. In metric terms, it is about 1.89 liters. This makes it an easy and practical unit to understand, especially for hydration and food measurements.
Summary Table: Half Gallon Measurements and Key Facts
| Category | Details |
|---|---|
| US Half Gallon | 64 fluid ounces |
| UK Half Gallon | 80 fluid ounces |
| Full US Gallon | 128 fluid ounces |
| Cups in Half Gallon | 8 cups |
| Pints in Half Gallon | 4 pints |
| Quarts in Half Gallon | 2 quarts |
| Metric Equivalent (US) | Approximately 1.89 liters |
| Metric Equivalent (UK) | Approximately 2.27 liters |
| Standard Water Bottle (16.9 oz) | About 3.79 bottles for 64 oz |
| 32 oz Bottle | 2 refills to reach 64 oz |
| Weight of Half Gallon (Water) | About 4.17 pounds (1.89 kg) |
| Hydration Rule | Common 64 oz guideline (not universal) |
| Women Daily Intake | Around 91 ounces total fluids |
| Men Daily Intake | Around 125 ounces total fluids |
| Hydration from Food | About 20 percent of intake |
| System Difference | US uses Wine Gallon, UK uses Imperial Gallon |
| Key Authority | National Institute of Standards and Technology (NIST) |
US vs UK Half Gallon Difference
The number of ounces in a half gallon changes depending on the system you use. In the United States, a half gallon is 64 fluid ounces. In the United Kingdom, which uses the Imperial system, a half gallon equals 80 fluid ounces.
This difference exists because the United States kept the older Queen Anne Wine Gallon from 1707, while the UK updated its system in 1824 to the Imperial Gallon. As a result, the UK half gallon is about 20 percent larger than the US half gallon.
Another interesting detail is that a US fluid ounce is slightly larger than an Imperial fluid ounce. A US pint equals 16 ounces, while a UK pint equals 20 ounces. These differences matter when you compare recipes, measurements, or product sizes between countries.
Understanding Common Conversions
Knowing how to break down a half gallon into smaller units helps in daily tasks. A half gallon equals 8 cups, which is useful for cooking and baking. It also equals 4 pints, which are often used in beverage servings. Since each pint is 16 ounces in the US, the math remains simple and consistent.
This structure comes from the United States customary system, which is maintained by standards such as those set by the National Institute of Standards and Technology. These conversions ensure that a half gallon remains the same across the country, whether you are in California or New York.
Bottle Math and Real Life Examples
Many people use water bottles to track their daily intake, so understanding bottle math makes the concept more practical. A standard single serve water bottle is often 16.9 ounces, which equals about 500 milliliters.
To reach 64 ounces, you need about 3.79 bottles of 16.9 ounces. In real terms, this means drinking three full bottles and about three quarters of a fourth bottle. Most people round this up to four bottles, which gives slightly more than a half gallon at 67.6 ounces.
Other bottle sizes also make the math simple. If you use a 32 ounce bottle, you only need two refills to reach a half gallon. If you use a 24 ounce bottle, you need just under three refills. These numbers help people stay consistent with their hydration goals.
Hydration and the 64 Oz Rule
The idea of drinking 64 ounces of water each day is very popular. It comes from the well known 8 glasses a day rule, where each glass is about 8 ounces. Together, this equals 64 ounces or half a gallon.
However, modern research shows that hydration needs are not the same for everyone. Factors such as body weight, activity level, gender, and environment all play a role. According to guidance often linked to organizations like the National Academy of Medicine and the Mayo Clinic, daily fluid intake can vary.
For women, total daily fluid intake is often around 91 ounces. For men, it is about 125 ounces. Another common guideline suggests drinking half your body weight in ounces. For example, a person weighing 150 pounds may aim for about 75 ounces per day.
Personalized Hydration in 2026
In recent years, especially around 2026, the idea of a fixed 64 ounce rule has shifted toward personalized hydration. Experts now suggest listening to your body and drinking when you feel thirsty. This approach works because the body has a natural system to maintain balance.
Hydration also comes from more than just water. About 20 percent of your daily fluid intake can come from food. Fruits and vegetables such as watermelon, cucumbers, lettuce, and celery contain a high percentage of water. These foods help support hydration without requiring extra drinks.
Even beverages like coffee and tea contribute to hydration. Although caffeine has a mild diuretic effect, the water content in these drinks still adds to your overall fluid intake.
Modern Bottle Culture and Smart Hydration
Hydration has become part of modern lifestyle trends, especially among younger generations. Many people now carry large reusable bottles as part of daily routines. Sizes like 32 ounces and 40 ounces are popular because they make it easy to reach a 64 ounce goal with just one or two refills.
The market has also introduced advanced hydration tools. Smart bottles can track how much water you drink and remind you to stay on schedule. Some models use LED lights to signal when it is time to drink. Others connect with apps like Apple Health or Fitbit to monitor your intake.
Innovations have gone even further. Some bottles use UV-C technology to clean themselves, while others use scent based systems to create the feeling of flavored water without adding sugar. These features show how hydration has evolved beyond simple measurement.
Weight of a Half Gallon of Liquid
A half gallon measures volume, but it also has weight. A half gallon of water weighs about 4.17 pounds, which is roughly 1.89 kilograms. This weight is often used as a reference point.
However, different liquids have different densities, so their weights vary even if the volume stays the same. Honey is much heavier and can weigh around 6 pounds for a half gallon. Maple syrup is also dense and weighs about 5.5 pounds. Milk is slightly heavier than water at about 4.3 pounds.
On the other hand, liquids like vegetable oil and gasoline are lighter. Vegetable oil weighs around 3.85 pounds for the same volume, while gasoline can be close to 3 pounds. This shows that volume and weight are not the same and should not be confused.
History and Myths Behind the 64 Oz Rule
The origin of the 64 ounce idea is often linked to a recommendation from 1945. It suggested that people should drink about one milliliter of water for every calorie consumed. For a 2000 calorie diet, this equals about 64 ounces. However, this guideline included water from food as well, which many people overlooked.
The measurement itself comes from older systems. The US gallon is based on the Wine Gallon from 1707, while the UK later changed to the Imperial system in 1824. These historical changes explain why the two systems differ today.
Another myth is that drinking all your water at once is effective. In reality, the body absorbs water better when you drink it slowly throughout the day. The kidneys can process only a certain amount per hour, so spreading intake is more efficient.
Risks of Overhydration and Modern Awareness
While staying hydrated is important, drinking too much water in a short time can be dangerous. This condition is known as hyponatremia or water intoxication. It occurs when excess water dilutes the sodium in your blood, which can cause serious health issues.
Modern awareness has also raised concerns about microplastics and chemicals like BPA found in single use plastic bottles. As a result, many people now choose stainless steel or glass bottles to reduce exposure and support environmental health.
Everyday Uses and Final Thoughts
A half gallon is not just a number. It plays a key role in daily life, from tracking hydration to measuring liquids in cooking and buying products like milk or juice. Many food and beverage companies use the half gallon as a standard size because it is practical and familiar.
Understanding how many ounces are in a half gallon gives you more control over your daily habits. Whether you are monitoring your water intake, comparing bottle sizes, or following a recipe, knowing that a US half gallon equals 64 fluid ounces helps you stay accurate and informed.
In the end, the concept is simple, but its applications are wide. From history and science to health and modern lifestyle trends, the half gallon remains one of the most useful and widely used measurements in everyday life.
FAQs
What is the exact number of ounces in a half gallon?
A half gallon in the United States contains exactly 64 fluid ounces. This is based on the US customary system where one gallon equals 128 ounces.
Is a half gallon always 64 ounces worldwide?
No, a half gallon is not always 64 ounces. In the United Kingdom, a half gallon equals 80 fluid ounces because it follows the Imperial system, which uses a larger gallon.
How many 16.9 oz water bottles make a half gallon?
You need about 3.79 bottles of 16.9 ounces to reach 64 ounces. In practical terms, most people drink 4 bottles to slightly exceed a half gallon.
How much does a half gallon of water weigh?
A half gallon of water weighs about 4.17 pounds or 1.89 kilograms. This weight can change if the liquid is different, since density varies between substances.
Is drinking 64 ounces of water a day enough?
Drinking 64 ounces is a common guideline, but it may not be enough for everyone. Your needs depend on factors like body weight, activity level, and climate.
What is the difference between US and UK gallons?
The US gallon contains 128 fluid ounces, while the UK Imperial gallon contains 160 fluid ounces. This makes the UK half gallon larger at 80 ounces compared to 64 ounces in the US.
Can you drink a half gallon of water at once?
It is not recommended to drink a full half gallon at once. Your body absorbs water better when you drink it gradually throughout the day.
Do foods count toward your daily water intake?
Yes, foods do count. About 20 percent of your daily hydration can come from water rich foods like fruits and vegetables, which support overall fluid balance.
Blog
How GCSE Tutors and Maths Tutors Help Students Improve Grades and Confidence

Many students struggle with maths at different stages of their education. Some find it difficult to understand concepts, while others lose confidence due to repeated mistakes. This is where GCSE tutors play an important role.
At the same time, maths tutors help students build a strong foundation, making even complex topics easier to understand with the right approach.
In today’s competitive academic environment, having the right guidance can make a significant difference. Whether a student is preparing for exams or simply trying to improve their understanding, structured support can transform their learning experience.
Why Students Struggle with Maths
Mathematics is not just about numbers — it’s about logic, patterns, and problem-solving. However, many students face challenges such as:
- Lack of clear explanation in classrooms
- Fear of making mistakes
- Weak foundation in basic concepts
- Fast-paced school teaching
- Exam pressure
Without proper support, these challenges can grow over time. This is why many parents turn to math tutor services to help their children catch up and stay ahead.
How GCSE Tutors Make a Difference

1. Personalized Learning Approach
One of the biggest advantages of working with GCSE tutoring professionals is personalized attention. Unlike classrooms, tutors focus on:
- Individual strengths and weaknesses
- Custom learning pace
- Targeted practice
This ensures students fully understand each topic before moving forward.
2. Strong Exam Preparation
Exams require more than just knowledge — they require strategy. With GCSE Tutors, students learn:
- How to solve past paper questions
- Time management techniques
- Understanding exam patterns
- Avoiding common mistakes
This structured preparation increases confidence and improves results.
3. Building Confidence Step by Step
Confidence plays a huge role in academic success. Many students know the answers but hesitate due to lack of confidence.
Through 1:1 tutoring packages, students:
- Ask questions freely
- Practice without pressure
- Gain clarity in concepts
Over time, this builds self-belief and reduces exam anxiety.
Role of Maths Tutors in Concept Clarity

Breaking Down Complex Topics
A professional maths tutoring approach focuses on simplifying difficult concepts such as:
- Algebra
- Geometry
- Trigonometry
- Probability
Instead of memorizing formulas, students learn the logic behind them.
Consistent Practice and Feedback
Regular sessions with a math tutor ensure:
- Continuous practice
- Instant feedback
- Correction of mistakes
This helps students improve faster compared to studying alone.
Flexible Learning Options
With the rise of online education, students now have access to:
- Online maths tutoring
- Flexible scheduling
- Access to experienced tutors globally
This convenience allows students to learn at their own pace without stress.
Importance of 1:1 Tutoring
Focused Attention
In 1:1 tutoring packages, the tutor focuses entirely on one student. This leads to:
- Faster understanding
- Better engagement
- Personalized strategies
Tailored Study Plans
Every student is different. A customized plan ensures:
- Weak areas are improved first
- Strong topics are reinforced
- Progress is tracked regularly
How IB and A-Level Tutoring Support Students
While GCSE is important, many students continue their academic journey with advanced programs.
IB Tutoring
IB tutoring helps students manage a challenging curriculum by:
- Explaining complex topics clearly
- Supporting Internal Assessments
- Preparing for final exams
Students also benefit from IB 1:1 tutoring, which offers personalized guidance.
A Level Tutoring
With A Level tutoring, students prepare for higher education by:
- Strengthening subject knowledge
- Practicing advanced questions
- Developing analytical thinking
AP and IGCSE Tutoring
Other academic programs such as:
also require structured preparation, where expert tutors guide students through difficult concepts and exam techniques.
Benefits of Online Tutoring
Modern education has made learning more accessible through online platforms.
Key Advantages:
- Learn from anywhere
- Flexible timing
- Access to expert tutors
- Recorded sessions for revision
Students preparing for retakes can also benefit from IB retakes support through online sessions.
How Tutors Help with Exam Strategy
Understanding content is important, but applying it correctly in exams is crucial.
Tutors help students:
- Analyze question patterns
- Identify key points in questions
- Structure answers effectively
- Manage time during exams
This is especially useful for students in MYP tutoring and IB Primary Years Programme, where foundational skills are essential.
Choosing the Right Tutor
Not all tutors are the same. When selecting a tutor, consider:
- Experience and qualifications
- Teaching style
- Student reviews
- Track record of results
A good tutor does not just teach — they guide, motivate, and support students throughout their journey.
Long-Term Academic Benefits
Working with tutors does not just improve grades — it builds skills for life:
- Critical thinking
- Problem-solving
- Discipline
- Time management
These skills help students succeed beyond exams.
Common Mistakes Students Make Without Tutors
Without proper guidance, students often:
- Memorize instead of understanding
- Skip difficult topics
- Avoid asking questions
- Practice incorrectly
Tutors help eliminate these mistakes early, saving time and effort.
Final Thoughts
Education is not about struggling alone — it’s about learning the right way with the right support. With expert guidance from tutors, students can overcome challenges, improve performance, and build confidence.
Whether it’s preparing for exams or strengthening concepts, the support of experienced tutors can completely transform a student’s academic journey.
FAQs
1. How do GCSE tutors help students improve grades?
GCSE tutors provide personalized learning, exam practice, and targeted support to help students understand topics and perform better in exams.
2. Are maths tutors worth it?
Yes, maths tutors help students build strong foundations, improve problem-solving skills, and boost confidence.
3. What is the benefit of 1:1 tutoring?
1:1 tutoring offers personalized attention, faster learning, and customized study plans based on the student’s needs.
4. Can online tutoring be effective?
Online tutoring is highly effective as it offers flexibility, access to expert tutors, and convenient learning from home.
5. How do tutors help with exam preparation?
Tutors teach exam techniques, time management, and provide practice with past papers to improve performance.
6. What subjects do tutors usually cover?
Tutors cover a wide range of subjects including maths, science, IB programs, A Levels, AP, and IGCSE.
-

 Biographies2 months ago
Biographies2 months agoWho Is Agnetha Larsson? The Untold Story of Zara Larsson’s Mother
-
 Celebrity7 months ago
Celebrity7 months agoWho Is Yeonmi Park’s Husband? Ex-Husband Ezekiel, Marriage, Divorce & Family Facts and More
-

 Celebrity5 months ago
Celebrity5 months agoCrispy Heaton – Musician, Father of Charlie Heaton & His Untold Story
-

 Celebrity7 months ago
Celebrity7 months agoWill Sonbuchner Wife: Inside Sonny Side’s Love Life & Private Marriage
-

 Celebrity3 months ago
Celebrity3 months agoWho Is Lily Aerin Savage? Learn About The Daughter of Actor Fred Savage
-
 Celebrity3 months ago
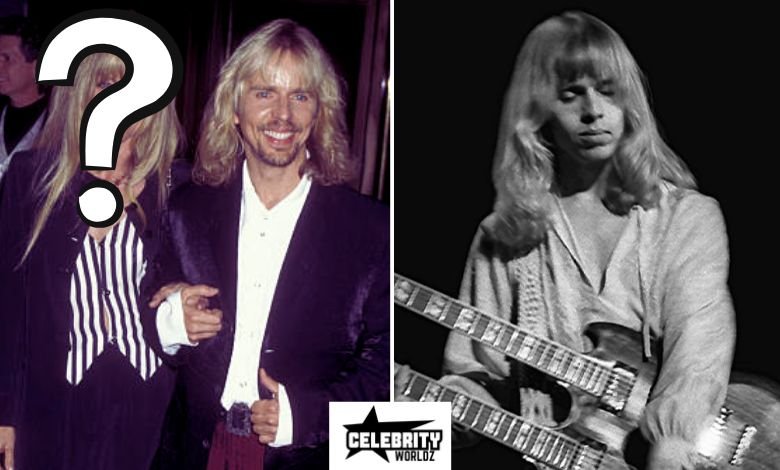
Celebrity3 months agoWho is Cuppy Enders? The Untold Story of Tommy Shaw’s First Wife
-
 Celebrity3 months ago
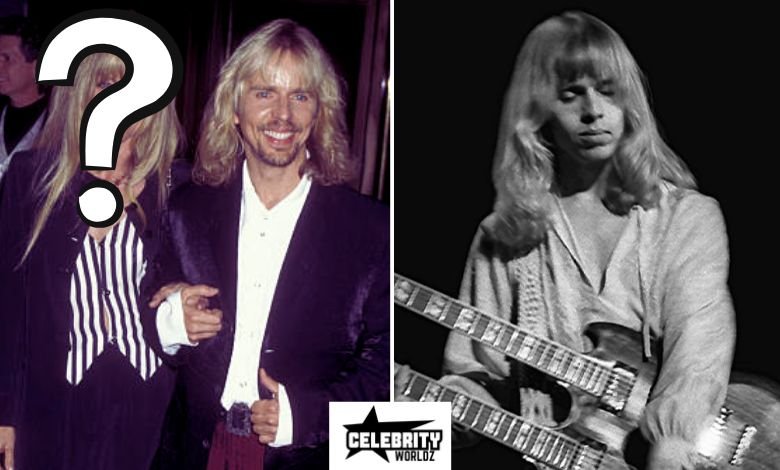
Celebrity3 months agoWho Is Sandra Purdy? The Life of Ken Osmond’s Devoted Wife
-
 Biographies1 month ago
Biographies1 month agoWho is Margaret Helen Jesse? The Story of Ted Cassidy’s Former Wife



